By | Abdul Wafi bin Abdul Rahman, Zainurrasyid bin Abdullah, Hafizah binti Che Hasan, Muhammad Fadzlan bin Zainal & Mohamed Fadzlee bin Sulaiman
Introduction
Sun Tzu once said, “If you know the enemy and know yourself, you need not fear the result of a hundred battles.” These words by Sun Tzu thousands of years ago can be implemented now in a cybersecurity era when there is a need for in-depth knowledge about attackers and our organisations to strengthen organisational defence. This technique is called cyber threat intelligence.
Intelligence is defined as first-hand information that leads to changes in behaviour. In cybersecurity, threat intelligence is evidence-based knowledge, including context, mechanisms, indicators, implications and action-oriented advice about an existing or emerging menace or hazard to assets. This intelligence can be used to inform decisions regarding the subject’s response to that menace or hazard [1]. Threat intelligence has now become a trend as cyberattacks are more sophisticated. However, most organisations are focusing on their threat intelligence capability only in the most basic use cases, such as integrating feed with IPS, firewalls and SIEM without taking full advantage of the context and insights of threat intelligence itself.
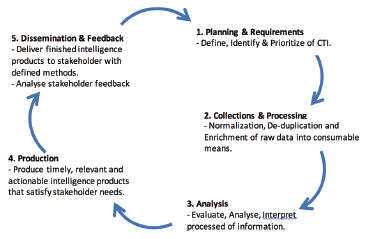
Cyber Threat Intelligence Process
Cyber threat intelligence gathers raw information about cyber threats from many different sources. It then analyses the collected information to produce appropriate threat intelligence reports. The fundamental purpose of this kind of activity is to keep companies informed on advanced threats, new exploits and zero-day threats to which they might be vulnerable and how to act against them. Figure 1 shows the lifecycle of Cyber Threat Intelligence (CTI), which involves planning and requirements, data collection and processing, data analysis, producing insights or actionable intelligence and dissemination of insights to the stakeholders.
Cyber Threat Intelligence Advantages
Implementing cyber threat intelligence can surely offer an organisation plenty of advantages. Here are some reasons why threat intelligence really matters:
-
Lowering Costs
Cyber threat intelligence can lower overall business expenses because first-hand information leads to mitigating an organization’s risk. The data breach of Equifax in 2017 cost the company over $600 million that included government investigations and lawsuits [3]. - Minimizing Data Loss
A cyber threat intelligence system helps prevent or block suspicious addresses from infiltrating the network and stealing sensitive data. - Maximizing Staffing
A threat intelligence system improves the efficiency of an organisation’s security team by correlating threat intelligence with anomalies flagged by tools on the network. A threat intelligence team can integrate threat intelligence into the organization’s foundation to lower security response time and allow the company staff to focus on other tasks. - In-Depth Analysis
Cyber threat intelligence really helps the organization analyse different techniques that have been used by cybercriminals. By analysing such cyber threats, the organization can determine a security defence mechanism to handle potential attacks. - Information Sharing
Threat intelligence information and reports could be shared with the threat intelligence community according to protective marking while protecting sources when required.
Levels Of Cyber Threat Intelligence
Cyber intelligence comes in many forms. Some cases are very urgent, some are merely informative, while others require technical knowledge and expertise. In this section, the U.S. Department of Defence (DoD) is used as a benchmark in approaching intelligence [4]. Based on DoD, intelligence can be categorised into 3 intelligence levels: strategic, tactical and operational, as shown in Figure 2.
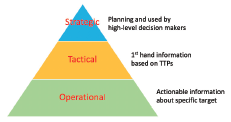
Strategic Intelligence
Strategic intelligence plays an important role in analysis and gaining information to help organizations understand the type of threat, motivation of threat, threat actor and likelihood of attack happening. All of this information enables a CTI team to plan and use the right resources for protecting and mitigating future threats.
Tactical Intelligence
Tactical intelligence includes first-hand information gained directly from the Tactics, Techniques, and Procedures (TTPs) of adversaries, whether internally or externally. This information is typically derived from real-time monitoring and may influence some of the tactical decisions for potential threats.
For instance, external sources reveal which domain has been taken over by an adversary malicious code. Internal monitoring sources confirm whether the organisation has been affected and which system has been infected with the malicious code.
Operational Intelligence
Operational intelligence is the day-to-day job of making decisions, allocating resources and prioritising tasks based on data and information. This includes trends of analysis, types and trends of attacks, technical direction of threat actors, adversaries of selected targets infected with viruses, and malicious Tactics, Techniques and Procedures (TTPs).
Besides, operational intelligence may include information and sharing feeds from other joint cyber intelligence from the local and international communities. It can also be useful to share, identify, analyse and remediate attacks on the network.
Cyber Threat Prediction

A source from Stanfield IT, an IT company in Australia, mentioned that almost half of all companies have sensitive information that is not protected. As the company focuses on healthcare, it is predicted that attacks on healthcare will increased by 400% in the year 2020 and cost of the cybercrime activity is expected to exceed $6 trillion by 2023. These statistics illustrated in Figure 3 show that cyber threats will continue to increase.
As threat complexity grows and becomes more sophisticated, threat intelligence no longer comes from web-scraping forums or honeypots. Instead, it ought to be a contextualized federation of internal forensics and network indicators coming directly from the backbone of the most capable infrastructures in the world, allowing enterprises to get ahead of the hackers [6]. Here is where a cyber threat intelligence team would fit in the current security team setup, and any insight coming from the CTI team will be useful to mitigate and prevent incoming threats.
Therefore, it is vital for security teams to develop the right skills and equip with the latest knowledge of threats. Developing a threat hunting and intelligence team and process is iterative. There is no endpoint. Thus, stay focused on steps that might help improve speed, accuracy and clarity. This will bring a defense strategy to a higher level of protection against the evolving behaviours of attacks. Besides the capabilities of a threat intelligence team, a threat intelligence system also requires an AI-powered security solution and real-time enterprise-to-enterprise threat intelligence sharing to help achieve more accurate and faster decision-making.
Conclusion
By understanding this concept, it is possible to gain an abstract view of how threat intelligence can be gathered from different disciplines in an information security organization with actionable data. This is only the tip of the iceberg. As organizations and technology grow more complex, it is necessary to have a process and capability established to grab data from multiple sources, aggregate it, and provide it to the team leads to act on. Cyber threat intelligence can empower organisations to work effectively and efficiently and can give them the advantage needed to manage threats before loss is incurred. However, it falls back on organisations to decide how they want to utilise the insight coming from cyber threat intelligence based on their core business and functions.