By | Ahmad Sirhan, Ahmad Khabir, Nurfaezah Hanis & Adam Zulkifli
What Is An Insider Threat?
An insider threat can be defined as an evil-intentioned threat that can be posed by people within an organization, like employees, former employees, vendors or business associates. These people are often associated with possessing confidential information on the organization’s security practices, data and computer systems, which can be used for malicious activities, such as sabotage, intellectual property theft, fraud and theft of commercially valuable information.
Insiders normally have elevated access and could potentially exploit sensitive information without anyone suspecting. Nonetheless, anyone can be an insider threat to an organization if they do not dispose, secure, or utilize sensitive information according to the organization’s policies and procedures.
What Motivates An Insider Threat?
Verizon’s 2019 Data Breach Investigations Report states that 34% of data breaches in 2019 were insider attacks; 71% of the breaches were motivated by money, while the second motivator was espionage or attempts to gain strategic advantage with 25%. The majority of insiders want to make quick, good money off the data they stole. Some insiders are driven by grudges with former employers or others purposely want to sabotage the organization for personal gains.
Types Of Insider Threats

PhoenixNAP outlined 3 types of insider threats: compromised users, careless users and malicious users, as shown in Figure 1. Compromised users are employees who do not know they are compromised, e.g. employee receives an urgent e-mail requesting to send information or personal data to the sender, or the user is required to click on a phishing link in an e-mail for accessing rewards, benefits, etc. In this way employees may not realize they are being manipulated thru phishing e-mail.
Meanwhile, careless employees are the biggest security threat. These are more vulnerable as targets of attackers. A scenario could be when a user leaves their computer unattended and without any security controls. A few minutes is enough to gain access. A recent study from Ponemon Institute showed that employees using mobile devices and commercial cloud applications continues to increase the endpoint risk significantly. Some of the respondents said they are allowed to use personal devices to connect to the network through Bring Your Own Device (BYOD) for instance. Thus, negligence increases the endpoint risk and can impact an entire organization.
Malicious users are the most despicable to organizations. They can be current or former employees, contractors or business partners who gain access to an organization’s network, system or data. They usually have legitimate user access to the system and wilfully extract data or intellectual property without permission.
In addition, credential thieves are considered an insider threat. They come in the form of hackers who steal credentials to gain inside access to the system. Many do not see credential thieves as insider threats. But let’s not forget that once outsiders gain access to a system, they are effectively acting as insiders. They are a danger operating from within the environment, hence they are very much insider threats.
Indicators Of Insider Threats

Detecting attacks is still possible even though all information security control has been developed. Some signs are easy to spot to take immediate action. A number of indicators can actually be considered as early prevention.
Figure 2 shows the common indicators of insider threats, which are large data or file transfers, multiple failed logins, incorrect software access requests, machine’s takeover and abuse by service account.
Impact Of Insider Threats
Insider threats remain among the key threats to cybersecurity organizations. In previous years, big cases were reported at Marriott and Tesla. Insider threat cases can also have costly impacts, such as what happened at Punjab National Bank and Suntrust Bank.
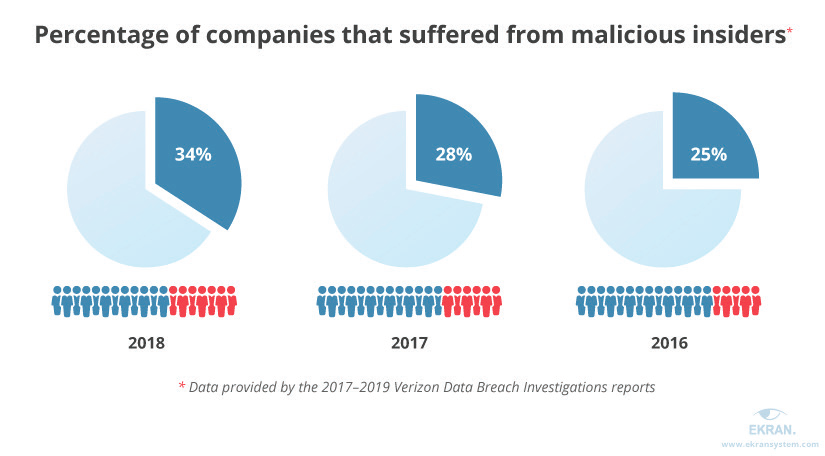
Figure 3 above depicts that according to Verizon 2019 Data Breach Investigations, 34% of breaches in 2018 were caused by insider threats. This was an increase of 6% from 28% in 2017. It is thus evident that the trend of insider threat-related breaches is rising yearly.
Proactive Approches To Counter Insider Threats
Using suitable systems and tools can raise the alarm for potential attacks. However, it is more effective to nurture a culture of securing information in the organization in the early stages. Organizations are encouraged to establish and maintain comprehensive approaches to protect the organization from intentional and unintentional harm. Below are a few proactive approaches that can help organizations to counter insider threats.
-
Establish a Security Policy
Establish a cybersecurity policy that actively protects against insider threat incidents but still enables staff to do their jobs efficiently and effectively. -
Screen New Hires
Having a background check of new hires could save the company a lot of hassle and prevent theft in the future. -
Employee Training and Awareness
- Security education and awareness should also be conducted throughout the year by having all employees including the management participate. This ought to increase commitment to creating a culture.
- Employees must also be trained effectively on the policies and training should be ongoing.
- Engage a workforce trained to recognize and report suspicious behaviour or activity.
-
Identify Trusted Insiders
Having an open dialogue with trusted insiders about why such policies are necessary and addressing their needs leads to collaborative cybersecurity. Then the employees are on board and motivated to protect the security of people and data. -
Use Multifactor Authentication
Implement strong, multifactor authentication measures to extremely sensitive systems within the company. -
Secure Desktops
There are a few services that a company can use to lock down desktops across the entire organisation. Such services are very beneficial especially in the case of careless employees.
Conclusion
It is clear that insider threats pose a significant problem to an organization’s information security. Proper and frequent education and training are key to mitigating insider threats. The people in the company should know about indications of insider threats and watch out for them. In order to help prevent accidental threats, users should be trained to be hardened against social engineering and to be extra careful with how they handle sensitive data.